
Your Rate Limiter Is Your Biggest Outage Risk
Why your rate limiter might be your biggest outage risk — and how to fix it with the right algorithms and architecture.
This site stores data to improve your experience. Learn more in our Consent Policy and Privacy Policy.
Microsoft cloud platform with AKS, Entra ID, DevOps pipelines, and Bicep IaC
Azure occupies a unique position in enterprise platform engineering because of its deep integration with Microsoft’s identity and productivity stack. Entra ID (formerly Azure AD) gives platform teams federated identity, conditional access, and workload identity federation out of the box—capabilities that take significant effort to replicate on other clouds. AKS provides managed Kubernetes with tight Azure networking integration, and Azure DevOps offers a mature CI/CD pipeline system that many enterprises already have in place.
For platform engineers, Azure’s strength is its enterprise governance tooling. Management Groups, Azure Policy, and Blueprints let you enforce guardrails across hundreds of subscriptions. Landing Zones provide prescriptive architecture for multi-team environments, and Bicep offers a cleaner infrastructure-as-code experience than ARM templates while remaining a first-party citizen. Combined with Terraform’s AzureRM provider, teams have real flexibility in how they define and provision infrastructure.
The challenge is navigating Azure’s layered service model and frequent rebranding. Services shift names, preview features graduate unpredictably, and the relationship between Azure DevOps and GitHub Actions continues to evolve. Successful Azure platform teams build abstraction layers that shield application developers from these shifts while still leveraging the platform’s enterprise integration advantages.

Why your rate limiter might be your biggest outage risk — and how to fix it with the right algorithms and architecture.

Quality gates that block too aggressively train engineers to bypass them. Here's how to design gates that catch real problems without becoming obstacles.
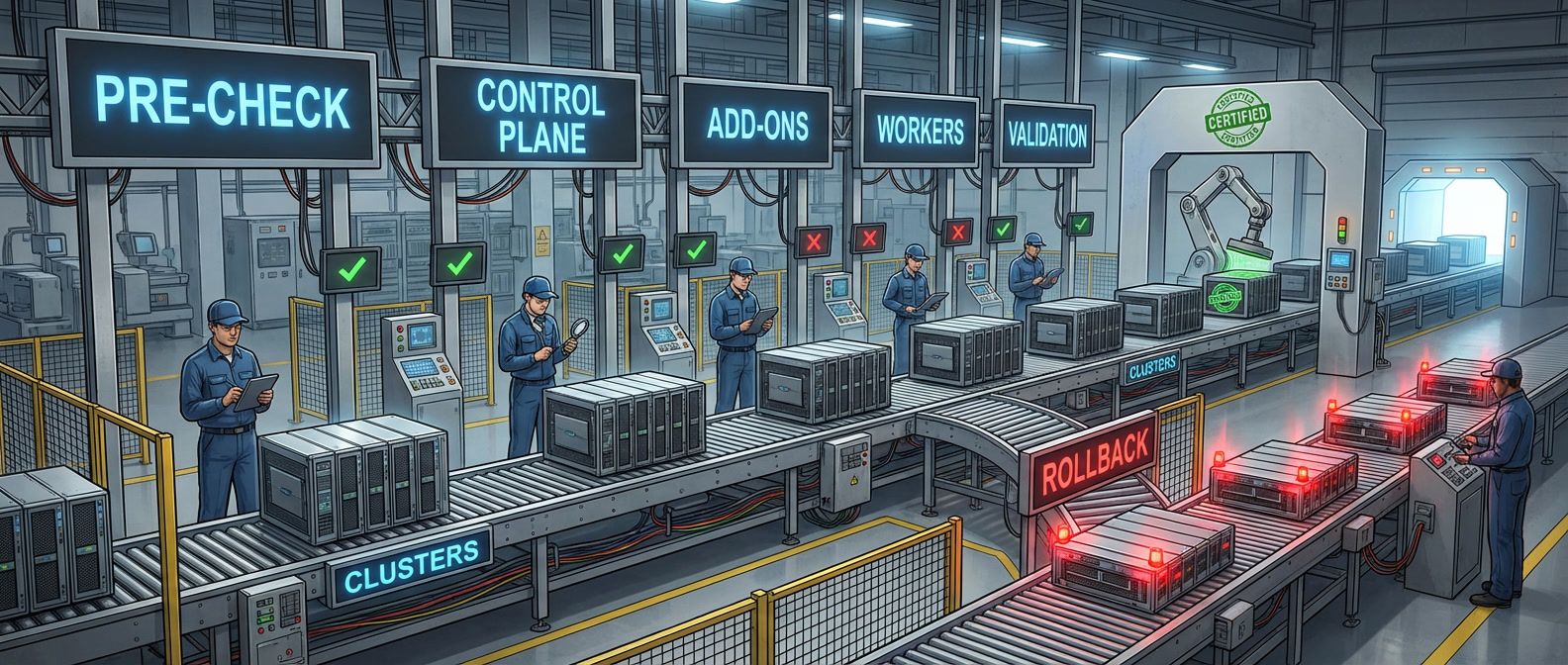
A playbook for cluster upgrades that minimizes risk through preparation, proper sequencing, and tested rollback procedures.
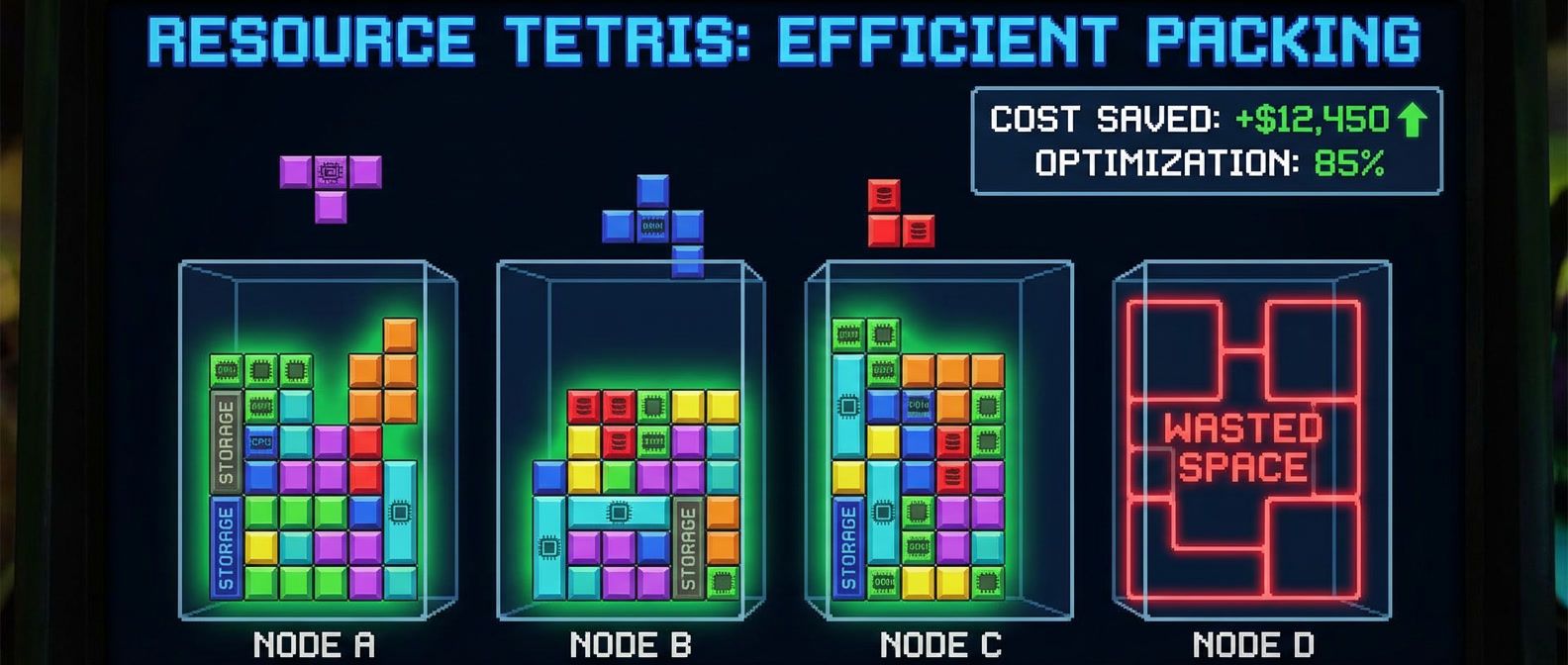
The boring resource decisions that actually determine your cloud spend on Kubernetes clusters.

Building only what changed with affected-based builds and remote caching that actually speeds up CI.

Shadow traffic testing and automatic rollback eliminate migration risk. Learn the observability-first approach that makes legacy modernization safe.
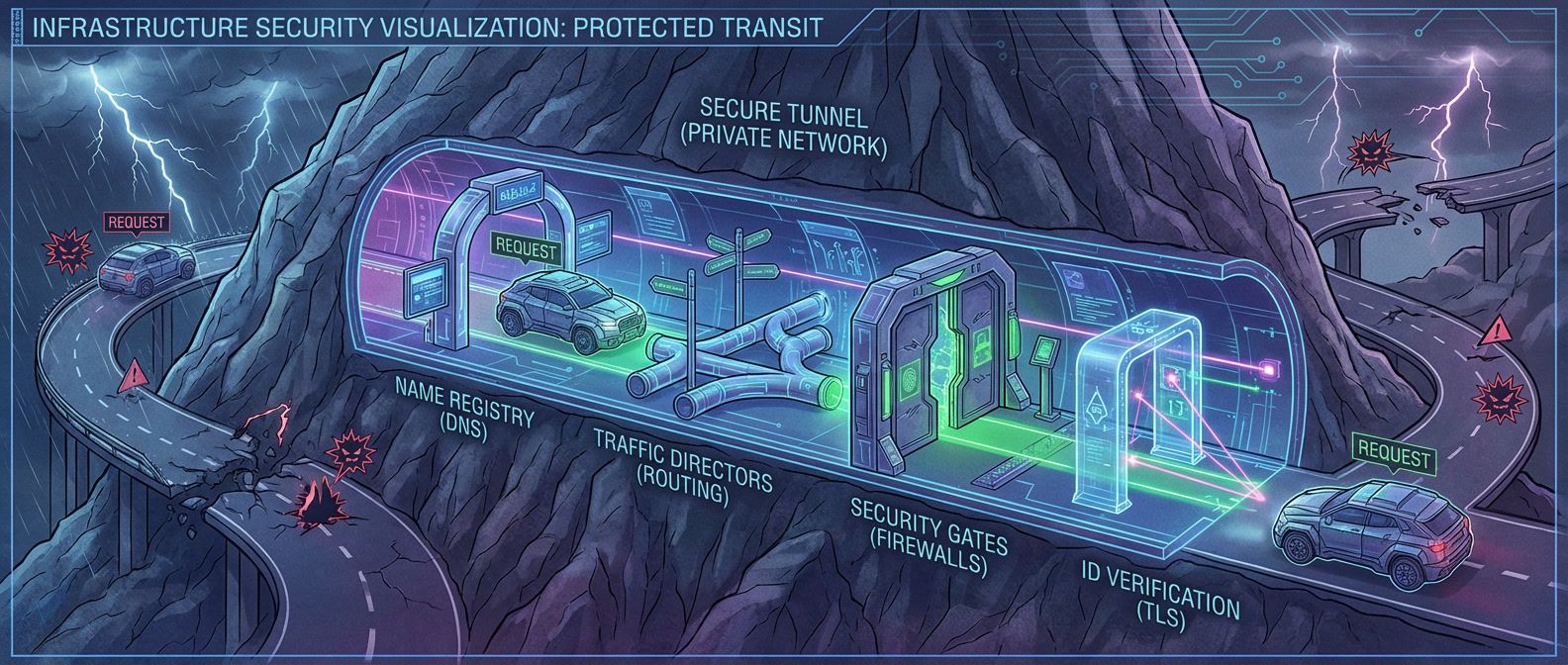
A systematic approach to debugging the networking issues that appear when services move to private connectivity.

Long-lived service account keys are the most common - and most preventable - cloud security vulnerability. Workload identity federation replaces static credentials with cryptographic proof of identity, eliminating an entire category of risk.
Recognize state corruption symptoms and apply the right recovery procedure: force-unlock for stuck locks, import for orphaned resources, backup restoration for severe corruption.
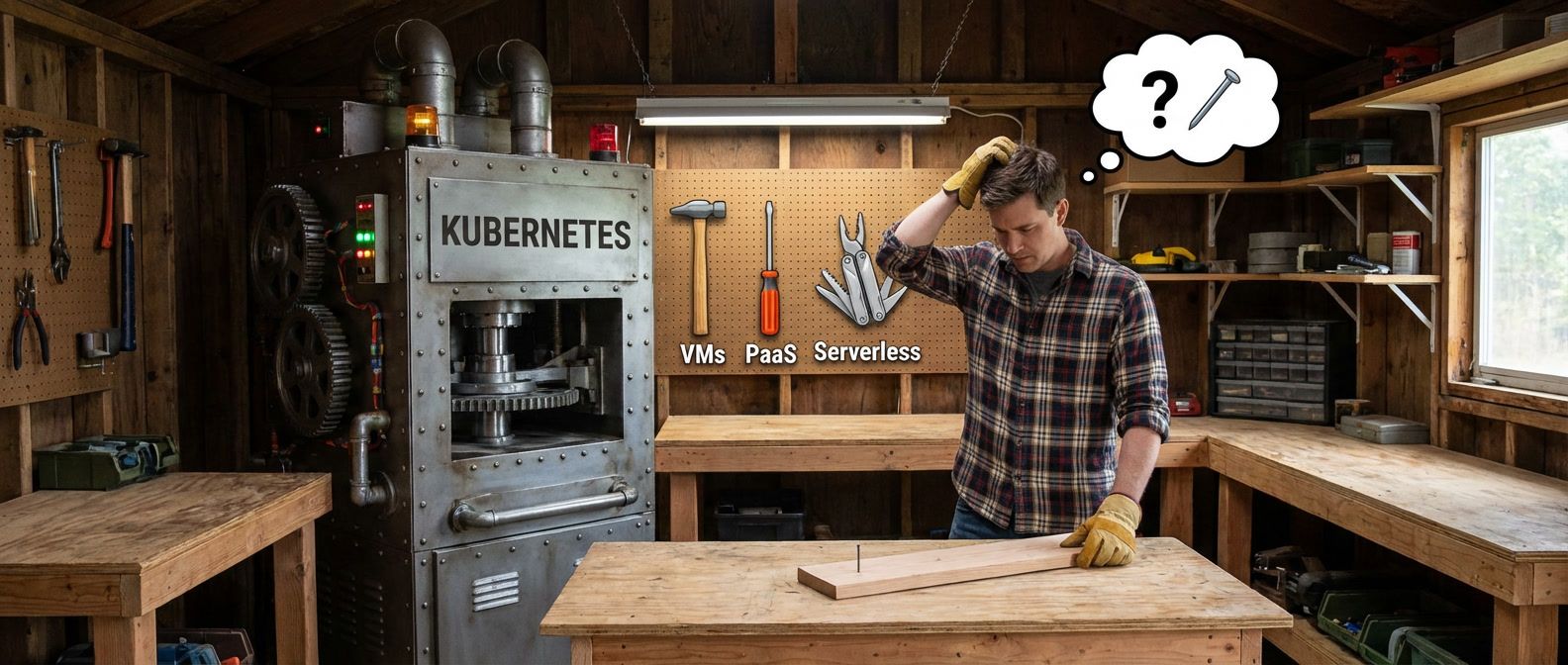
A practical framework for evaluating whether Kubernetes fits your organization's needs, including hidden costs, team requirements, and a decision scorecard.
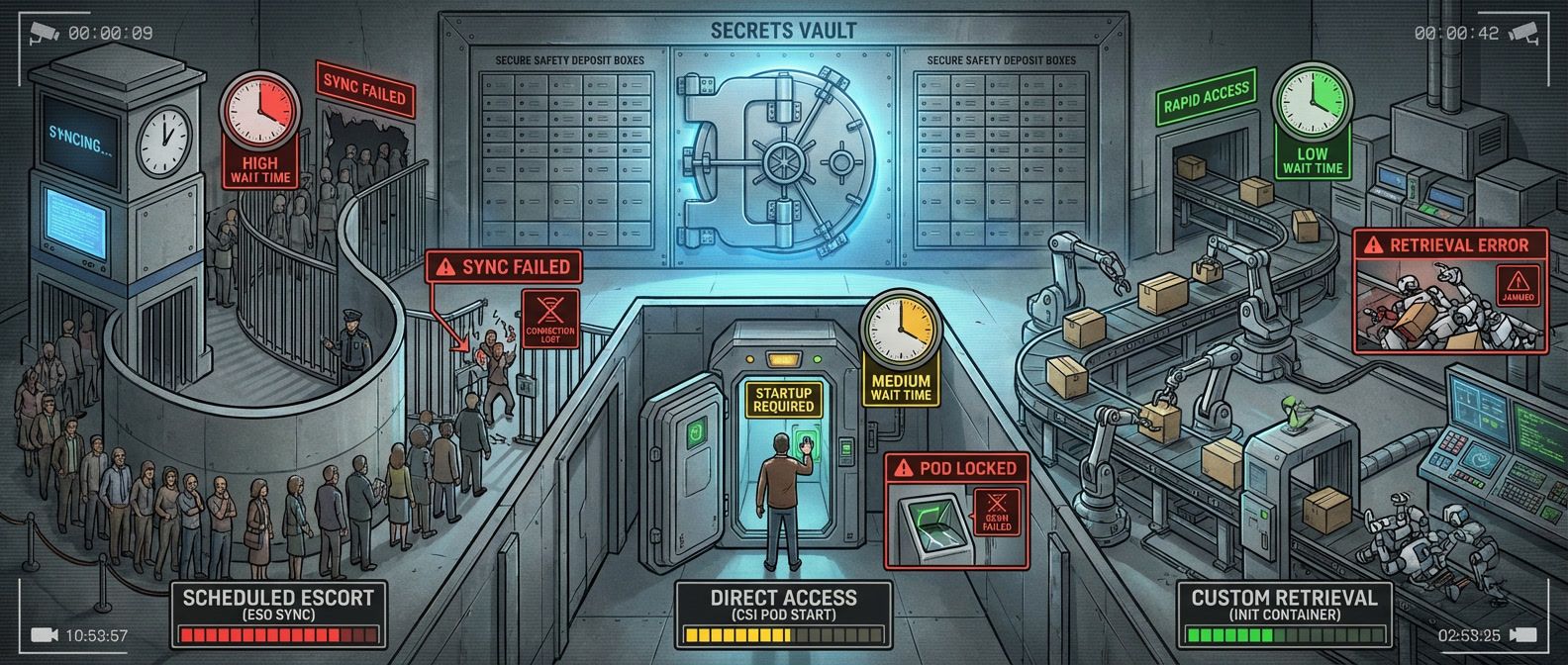
ESO vs CSI Driver: understanding which failure mode you've chosen before it matters.