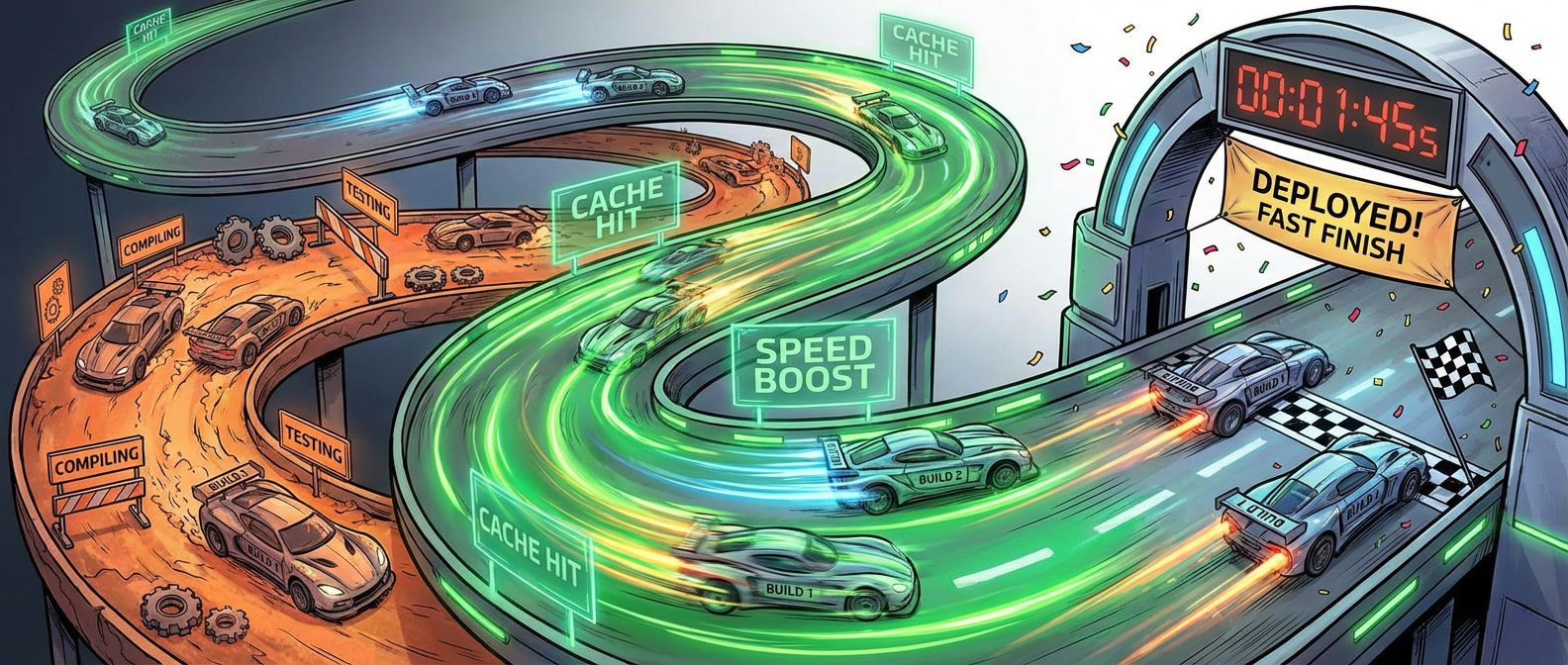
Why Your CI Cache Misses Everything (And How to Fix It)
Cache keys, Docker layer ordering, and the pitfalls that turn caching from a speedup into a source of production bugs.
This site stores data to improve your experience. Learn more in our Consent Policy and Privacy Policy.
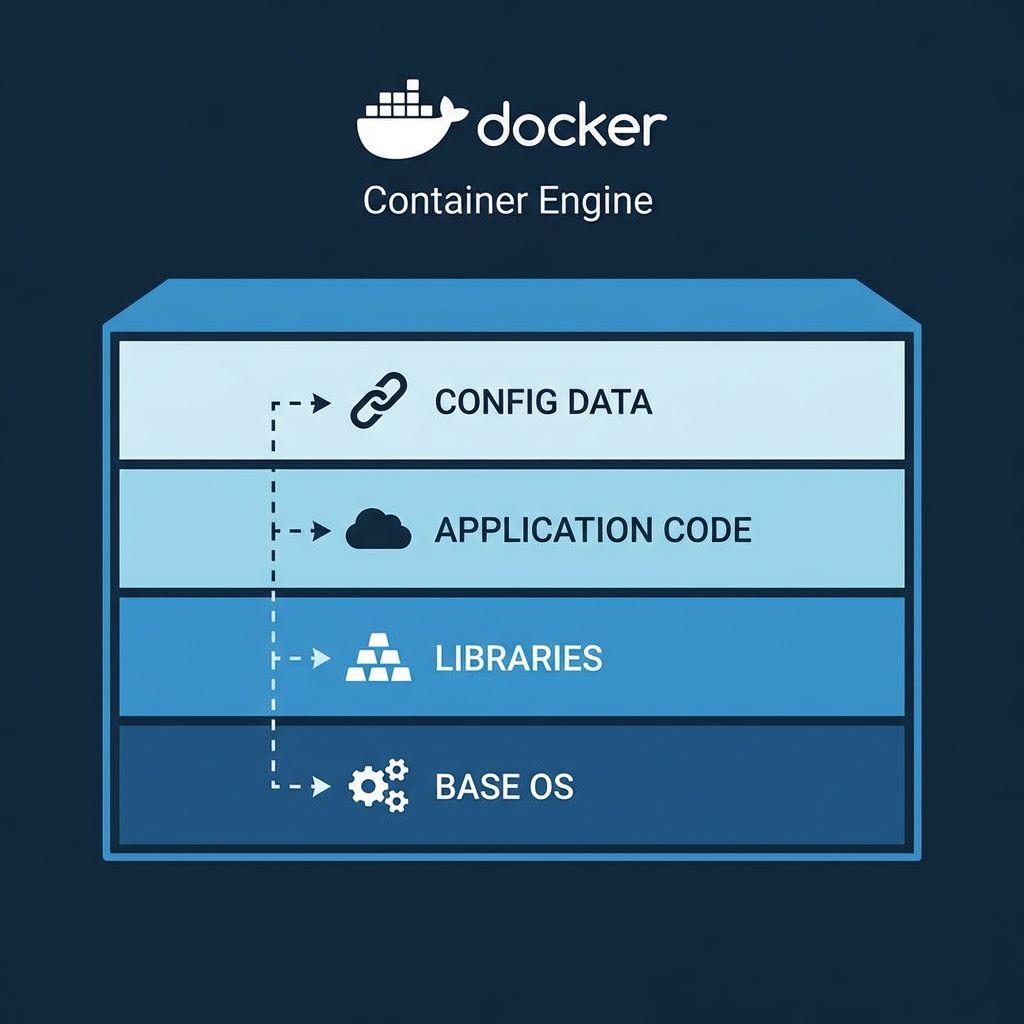
Container images, multi-stage builds, and reproducible packaging for all environments
Docker changed how platform engineers think about deployment artifacts. Instead of configuring servers to match application requirements, teams package applications with their exact dependencies into images that run identically everywhere. Multi-stage builds keep production images lean, BuildKit caching speeds up CI pipelines, and OCI-compliant registries give organizations a standard way to store and distribute artifacts across environments.
For platform engineering, Docker sits at the foundation layer. Golden-path Dockerfiles enforce security baselines—non-root users, minimal base images, pinned package versions—before code ever reaches a cluster. Build pipelines scan images for CVEs, sign them with cosign or Notary, and push to private registries with promotion policies that gate what reaches production. The container image becomes the unit of trust between development teams and the platform.
Docker’s role has shifted as Kubernetes handles orchestration and containerd runs workloads directly. The Docker CLI and Compose remain essential for local development, letting engineers run multi-service stacks on their laptops with a single command. Understanding image layering, build context optimization, and runtime security constraints still matters daily—even in environments where Docker Engine itself never touches a production node.
Cache keys, Docker layer ordering, and the pitfalls that turn caching from a speedup into a source of production bugs.

Building only what changed with affected-based builds and remote caching that actually speeds up CI.
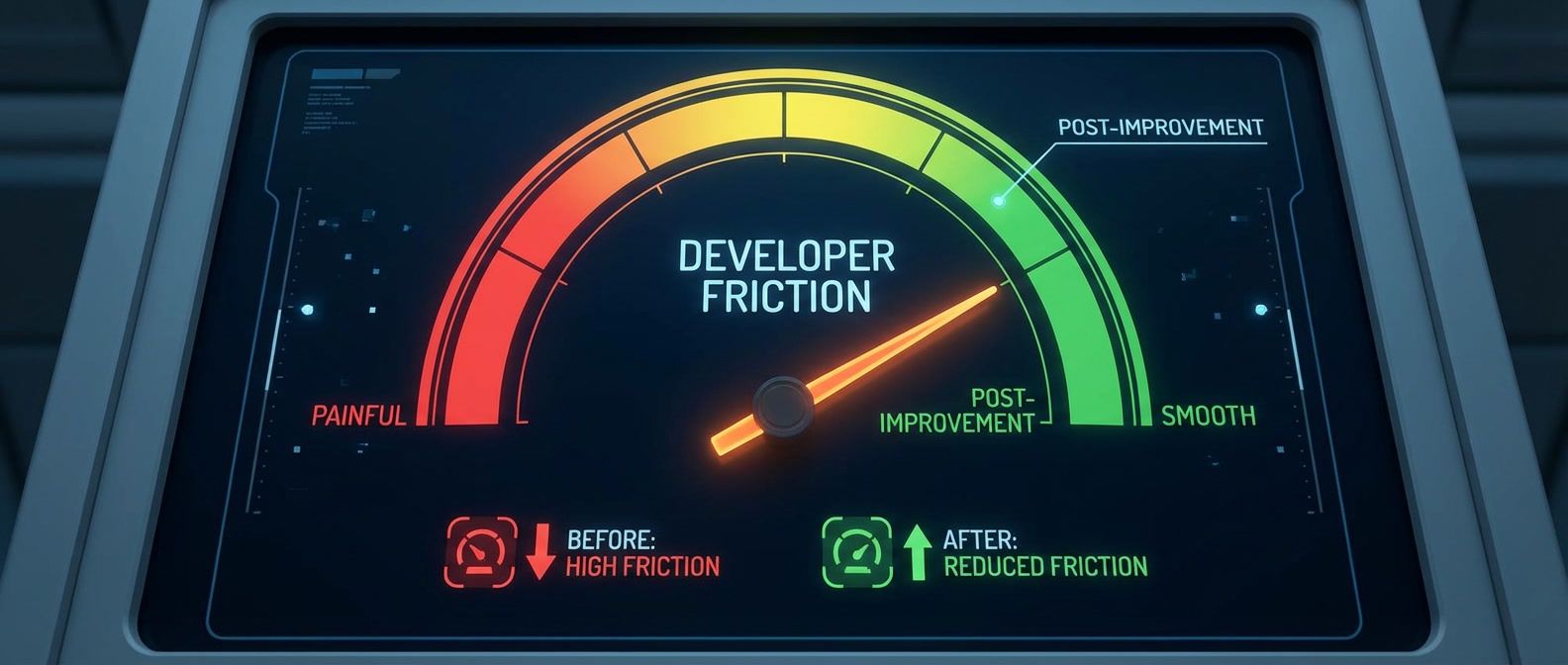
Lead time, onboarding time, and ticket deflection metrics that show whether your platform reduces friction.

EOL runtime upgrades stall on dependencies you don't own. Here's how to identify blockers, handle abandoned packages, and force version resolution when you're stuck.

Balancing standardization with team autonomy so the right thing is easy but not the only option.

Consumer-driven contracts catch breaking API changes at PR time, not in production. Here's how to escape the integration test trap.

Implement meaningful supply chain security without managing keys or paying for tooling. Learn keyless signing with Cosign and enforce verification at deployment time.

Implementing infrastructure policies with OPA and Conftest that catch violations before they reach production — starting with pre-commit hooks that run in under two seconds.

The fix isn't better scanners — it's better policies. Configure vulnerability scanning that reports actionable findings instead of overwhelming noise.